Updated, Sep. 8th 2023
This article gives you the best WordPress Security Tips 2023 and is intended for advanced WordPress website owners who want to make their website more secure. Since we’re talking about with basic principles of web servers, administrative tasks, and web technologies, ideally you are already familiar with them. If this is not the case and you don’t want to deal with technical details, feel free to contact us for a free consultation.
As web security specialists, we are often asked how to achieve 100% protection for IT systems and applications. The answer is simple: any (and we really mean any) IT system can be hacked. The reason for this is not the actual security systems. Modern systems do an excellent job when well maintained and properly operated. Rather, it is the human factor that often causes security risks. Simple examples of this fact are outdated systems, poorly programmed software or insecure passwords.
Our professional advice is therefore to prevent security risks as much as possible and, above all, to educate about what risks exist and what you can do as a website owner or simply as a user to achieve maximum IT security.
Lost password? Website hacked? Performance problems?
Get quick help via e-mail or WhatsApp!
WordPress Security Tips 2023
How secure is WordPress per default?
Immediately after installing the latest version and without using extensions (plugins) and templates (themes), WordPress offers a certain level of security. For example, the WordPress dashboard (the administrative area where content and settings are managed) is password protected by default.
However, what is shocking is that the unauthorized access can be observed immediately after WordPress installation using special network monitoring tools.
The techniques of hackers and bots are different, but they almost always have one goal: to break into your website. You are well advised to set up the highest possible security from the very beginning.
When it comes to WordPress security, there are a lot of things you can do to secure your website so that unwanted hackers can’t get into your beloved website. The last thing you want is to wake up one morning and find your website damaged.
That’s why we’re going to share here the best WordPress Security Tips 2022 that you can use to improve WordPress security and stay protected.
Web security? Isn’t the hoster responsible for that?
Many web hosting providers entice with low-cost packages, which usually include the WordPress CMS. In a survey, we found that performance is the most important factor in many cases when it comes to finding the right provider.
But what about security? In the same survey, we concluded that customers are sure that security is the responsibility of the provider. Unfortunately, this assumption is wrong when it comes to the website!
Of course, hosting providers take care of securing their own server infrastructure. However, this usually only concerns the systems that work in the background. These include, for example, web servers (Apache or Nginx), database servers (e.g. MySQL) or the hosting backend where you log in to manage your hosting package and plans.
The individual web application layers (presentation layers), to which your WordPress application belongs, are usually excluded from this. As a customer, you are responsible for increasing security beyond the default level set during WordPress installation.
What are the most common, malicious attacks and techniques used by hackers and how can I protect myself against them?
Brute force login attempts
Brute force login attempts use automated scripts to exploit weak passwords and gain access to your website. Using this technique, hackers can easily compromise tens of thousands of websites in a single day.
Threat elimination
Follow the instructions in this post. By doing so, you will stop this threat immediately and reduce future attacks to an absolute minimum.
Prevention
Setting up two-factor authentication, limiting login attempts, monitoring unauthorized logins, automatically blocking suspicious IPs, smart user management and using strong passwords are simple and very effective measures to keep intruders out. Most of this can be set up and configured with the help of a security plugin like WordFence with integrated web application firewall (WAF).
Moreover, it is possible to hide the WordPress default login page, which is the most common target. We’ll show you how to do that later in this post.
Backdoors
A backdoor vulnerability enables hackers to bypass security mechanisms and gain access to WordPress websites via abnormal methods. Once exploited, hackers can wreak havoc on hosting servers, for example, through contamination attacks, compromising multiple websites on the same server.
Backdoors are often disguised to look like normal WordPress system files. Vulnerabilities and bugs, especially in outdated versions of the platform, allow access to WordPress databases, the brain of your website where valuable data is stored.
Threat elimination
Fortunately, it is relatively easy to prevent and eliminate backdoors, as they are relatively easy to detect. You can scan your WordPress website with free tools like Sucuri SiteCheck, which can detect common backdoors.
Prevention
Setting up two-factor authentication, blocking suspicious IPs, restricting admin access including assigning strong passwords, and most importantly, preventing unauthorized code from running on the server can easily eliminate common backdoor threats. You will understand how to do this later in this post.
SQL code injection (SQLi)
SQLi is the exploitation of a vulnerability related to SQL databases. The vulnerability is caused by negligent programming in a WordPress component (e.g. plugin) that accesses the database. This allows a hacker to inject database commands and potentially read additional data from the database, manipulate or delete data without authorization, or even take control of the entire database server.
Threat elimination
SQL injections are notoriously difficult to detect because they leave no traces on the server. Instead, the exploit executes real queries to the database. Therefore, most attacks are not detected until it is too late. Often, the only thing that helps is to import a clean backup. Therefore, the best protection is prevention.
Prevention
Keep WordPress, Themes and Plugins up to date and use trusted themes and plugins only. Use a web application firewall (WAF). Follow the tips, in this post.
Malicious redirects
Malicious redirects inject redirect codes into WordPress websites. The redirects are often placed in encrypted form and redirect web traffic to malicious websites. These include the so-called pharma hacks that hijack your website and redirect it to websites that offer pharmaceutical products. Pharma hacks are classified as spam by Google, which can cause your website to disappear from search results.
Threat elimination
Use a security plugin like Wordfence and scan the website. Follow the instructions in this article. If the threat still cannot be removed, contact us.
Prevention
Keep WordPress, Themes and Plugins up to date and use trusted themes and plugins only. Use a web application firewall (WAF). Follow the tips, in this post.
Cross-Site Scripting (XSS)
XSS means that a malicious script is injected into your WordPress website. The hacker uses this to send malicious code to your website visitor without their knowledge. The purpose is usually to collect and manipulate unauthorized data.
According to website security software vendor WordFence, cross-site scripting vulnerabilities are by far the most common vulnerability in WordPress plugins.
Threat elimination
Run a malware scan and try to locate and eliminate the threat. Pentest Tools offers an online scanner for this purpose. An XSS attack can attack the website in many different ways, and the removal can turn out to be like the endless search for a needle in a haystack. That is why we cannot emphasize enough how important it is to perform regular backups. Often this is the relatively easier and cleaner solution.
Prevention
Keep WordPress, Themes and Plugins up to date and use trusted themes and plugins only. Use a web application firewall (WAF). Follow the tips, in this post.
DDoS Denial of Service Attacks
DDoS exploits vulnerabilities and flaws in code to overload website operating system memory. This brings the website to a complete standstill for the duration of the attack, as the server is overloaded with the number of requests.
Hackers have compromised millions of websites and made millions of dollars by exploiting outdated and buggy versions of the WordPress software with DDoS attacks.
Even the latest installations of WordPress software do not provide complete protection against high-profile DDoS attacks.
Prevention
Below you will learn what you can do and why it is important to use a premium DNS provider to increase your WordPress security.
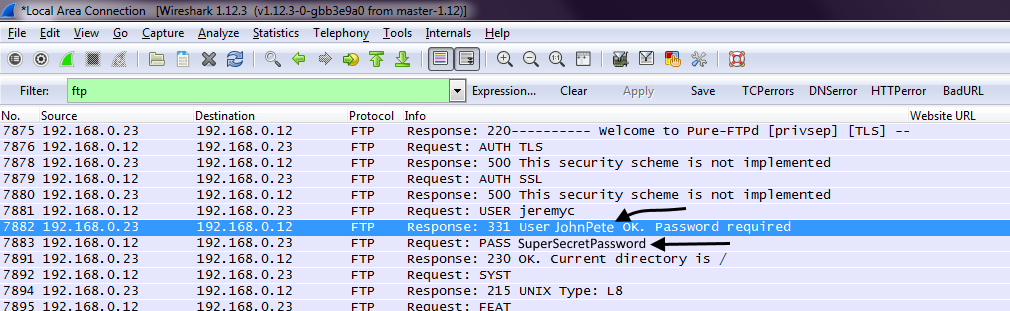
Man in the Middle Attacks (MitM)
There are several hacking techniques that are characterized as MITM attacks. All of them have one goal: to intercept, spy and possibly manipulate sensitive data between 2 communication points (e.g. your browser and your WordPress backend).
In the context of WordPress, one of the most common types of attack is session hijacking. In this, hackers gain control of your browser cookies, small data packets in which your website information is stored while you access WordPress. This gives the hacker access to a range of data, including your login credentials.
MitM attacks are often difficult to detect. Often, you do not even know that you have been affected. Therefore, the best protection is prevention.
Prevention
- Always pay attention to encrypted communication (https://)
- If possible, do not transmit sensitive data in public networks, such as cafes or airports
- If possible, use two factor authentication
- Keep your browser and operating system always up to date and use a good virus scanner
WordPress Security Tips 2023
According to a report by Forbes, on average, 30,000 new websites are hacked every day.
As for WordPress sites, it is estimated that at least 13,000 WordPress websites are hacked per day. However, it is important to note that these numbers are estimates and the actual number of hacked websites may vary.
1. Secure WordPress Hosting
WordPress security involves much more aspects than just protecting your website from unauthorized access. Security is also important at the level of the web server your WordPress hoster is responsible for. Besides our partners Mittwald and Niagahoster, there are certainly many others that do a great job not only in terms of performance.
When making your choice, pay attention not only to price and performance, but also to how secure your hoster is rated. If you don’t have technical knowledge of web server management, we strongly recommend that you opt for a conventional hosting package.
In many cases, hosters offer so-called VPS (Virtual Private Server) to run your application there. VPS offer great flexibility, but at the same time you are responsible for everything. Not only for your website. Therefore, VPS management requires appropriate, in-depth, technical knowledge, which you should only entrust to a specialist.
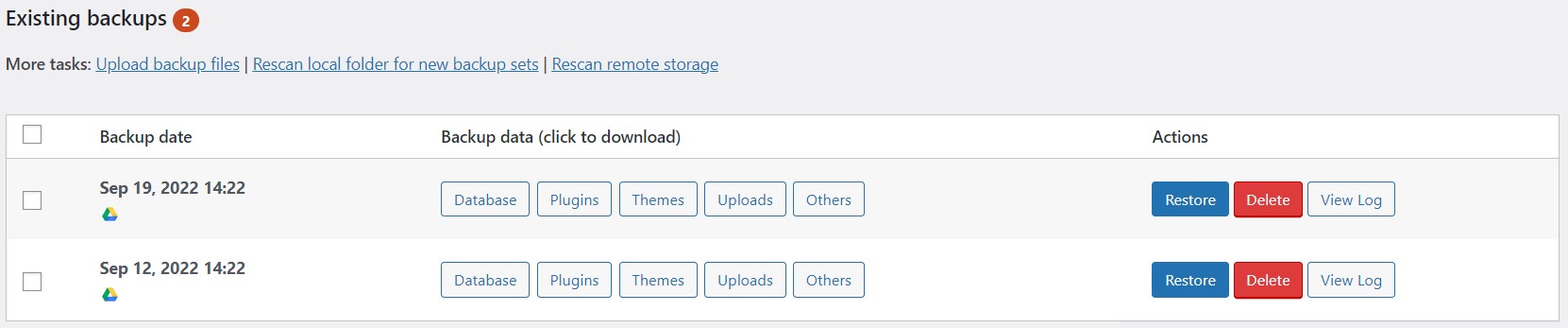
2. Regular Backups
Backups are meant for situations when a certain, usually very serious, problem can only be solved by restoring data. For this reason, we like to call them life insurance for websites. In case of a serious attack or if you yourself are responsible for a failure of your website, you can restore an older version with a few clicks.
Therefore, we advise you to always make regular backups so that you are prepared for the worst-case scenario. The frequency depends on how often data is changed.
Many hosting providers offer built-in backups that can be either automated on a daily basis or performed manually.
Another way to play it safe is to use WordPress plugins. Updraft is especially worth mentioning here. The free version already offers excellent features for automated backups. So you can easily specify the location (e.g. FTP, Amazon S3, OneDrive, Google Cloud Storage, Google Drive or Dropbox), the frequency and the number of backups.
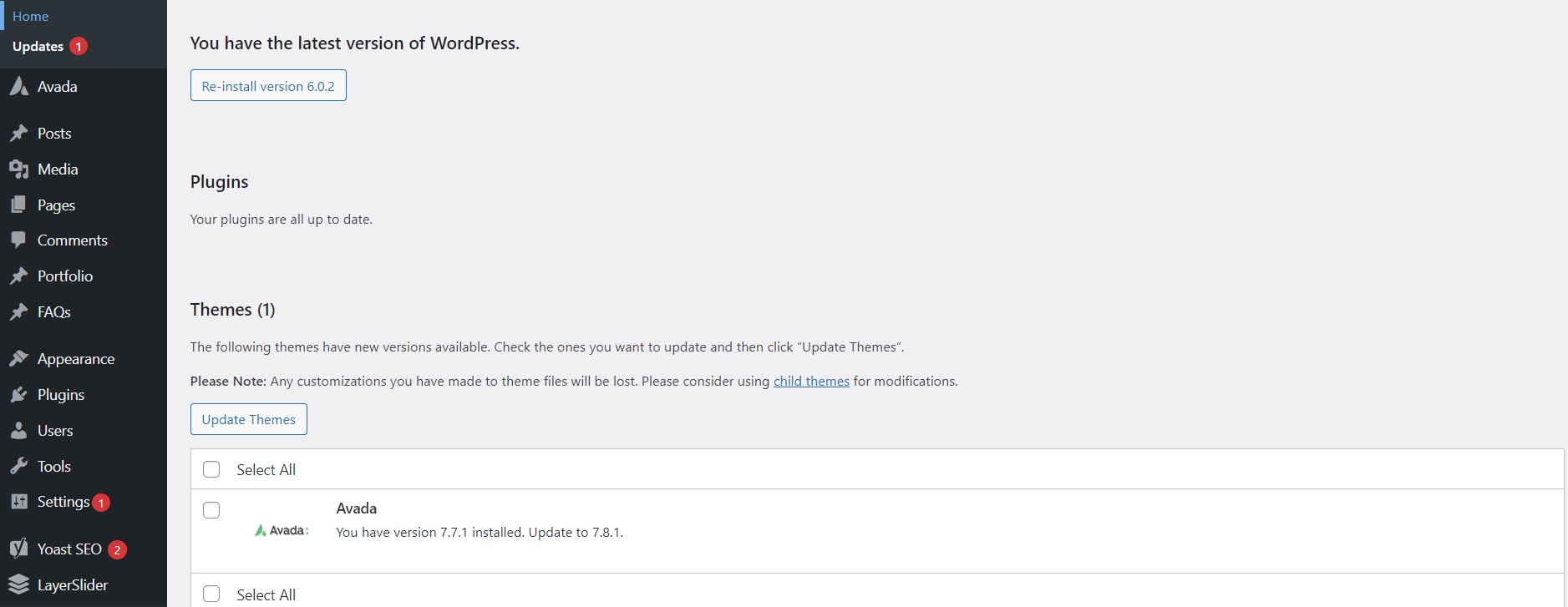
3. Regularly Update WordPress, Plugins and Themes
According to a Wordfence study that surveyed over 1,000 WordPress site owners who became victims of attacks, plugin vulnerabilities were found to be 55.9% of known entry points for hackers.
WordPress itself, plugins and themes are regularly updated by developers in terms of security, bugs or performance. In addition, updates ensure the compatibility of the respective components with each other.
Important: We recommend creating a backup of the entire web application before each update
Tools such as Updraft (WordPress plugin) or Softaculous (cPanel backend) are suitable for this purpose. With the latter, you even have the possibility to set up a so-called staging environment, which contains an exact copy of your live website. On this you can make any changes and test them extensively. With a few clicks, you can then import the changes you’ve made into your live site.
When there are updates for WordPress, plugins and themes, you see a notification in your WordPress dashboard.
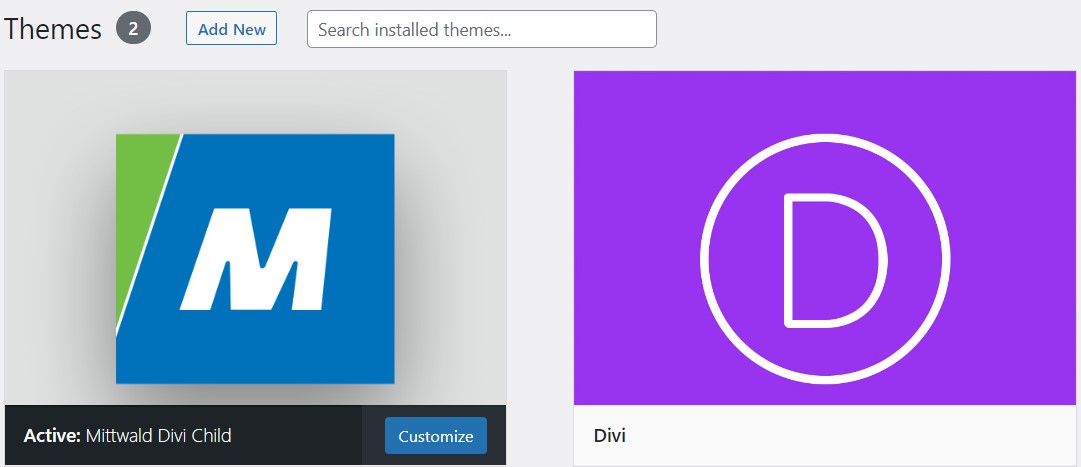
4. Plan Ahead
What features do you really need on your website? It’s often wiser to choose premium plugnis and themes like Divi or Avada in the beginning, as they already have a huge selection of features that you would otherwise have to cover with additional plugins. You also get good technical support, regular updates and the large communities are helpful.
In general, we recommend installing as few plugins as possible and making sure they are trustworthy. Never use so-called “nulled” plugins or themes, as they often contain malicious code.
5. User and Password Management
Use complex (strong) passwords
We can’t stress it enough: Use strong (strong) passwords. This is one of the easiest and most secure ways to improve WordPress security.
You may say: “they are too complicated, and I can’t remember them.” Just store your passwords in a vault on your computer. Tools like Bitwarden (free) or 1Password are great for this and even sync your passwords between multiple devices. They also include generators for usernames and passwords.
With WordPress Security Software like the Wordfence plugin, which we’ll discuss in more detail later, you can even enforce complex passwords.
Avoid storing important passwords in browsers. It’s convenient, but insecure. The popular Chrome browser in particular keeps making headlines and is responsible for one of the largest amounts of passwords ever stolen, with an incredible 8.4 million passwords in a single action.
Usernames
Never use the default username “admin” in your WordPress installation, as this is the most popular target for brute force attacks. Don’t make it too easy for the hacker. If the username is known, all you need is the password. If this is also easy to guess, the door is open to the attacker.
If the default user “admin” exists
- create a new WordPress username for the administrator account with a secure password in the user management in the WordPress dashboard.
- log out and log back into WordPress with the new user and delete the “admin” user.
- make sure you select “Assign all content to” option while deleting and assign it to your new admin.
6. Two-Factor Authentication (2FA)
You probably already know 2FA from other applications, and it’s easy to enable in WordPress as well. It is a two-step process that requires not only your password, but also a second login method.
A plugin like Wordfence lets you set this login method individually for each user.
This makes brute force attacks useless for the hacker, as it is almost impossible for the attacker to get both your password and access to your phone.
After you enable 2FA, you will usually have an additional input field on your WordPress login page where you can enter your security code or scan a barcode.
Take advantage of two-factor authentication as it is an easy way to greatly improve your WordPress security.
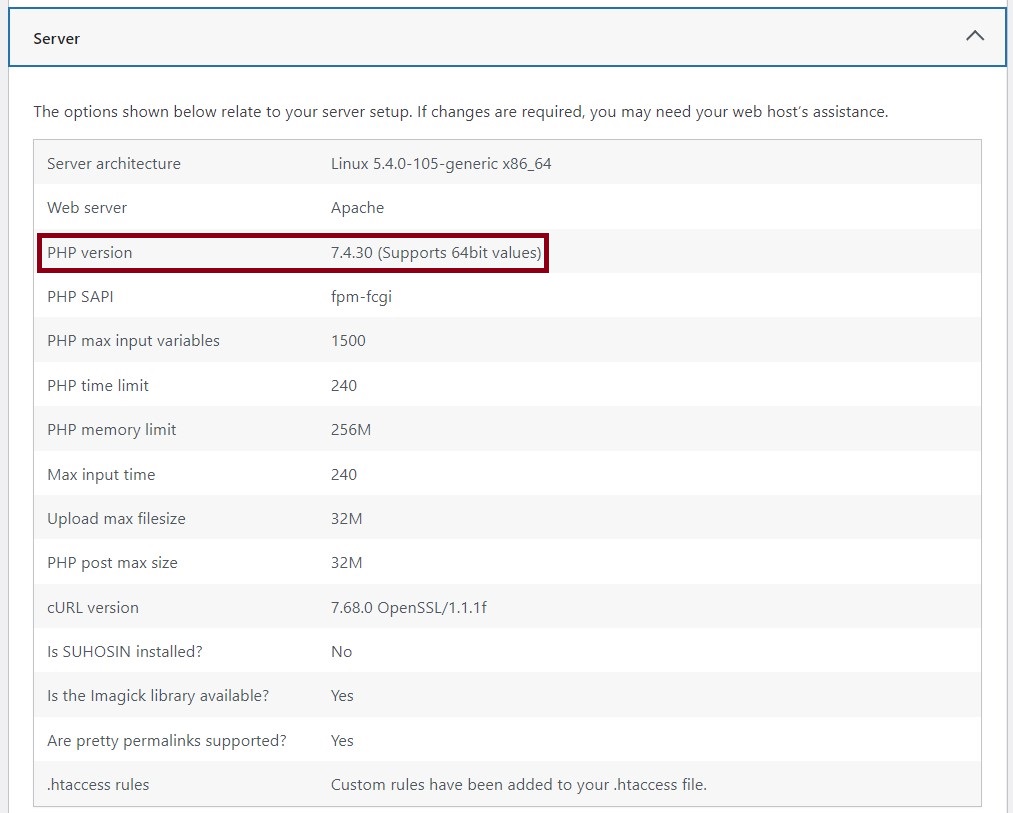
7. PHP Version
A website consists of HTML (page structure), JavaScript (small utility scripts that usually run in the user’s browser), CSS (responsible for formatting the content), as well as text and media files (content). These page elements are dynamically compiled (generated) by PHP when a user browses a page.
PHP is a programming language that runs on the web server and is responsible for the logic of the website. It forms the backbone of your WordPress site and is therefore a very important component.
Use a recent version (7.4 or 8.0) as it offers the highest level of performance and security through constant improvement and maintenance. There is no longer security support for PHP version 7.1 or lower, so your site is exposed to unpatched security vulnerabilities.
According to the official WordPress statistics page, over 57% of WordPress installations are still running PHP 5.6 or lower. Along with PHP 7.0, around 77.5% of WordPress websites are currently using PHP versions that are no longer supported.
You can find out which PHP version you are using in the WordPress dashboard under > Tools > Site health > Info tab > Category Server.
Usually, you can change the PHP version through the web administration interface of your web host.
If you are not sure, we will be happy to assist you!
8. Login Area
Just like with default usernames, hackers know the default address for the WordPress login area. For this reason, it is also a popular target for attacks. Make it harder to access the login area by changing your default login area URL and restricting login attempts.
How to change your WordPress login URL
We keep seeing the free WPS Hide Login plugin being promoted in this context. We don’t recommend this, as it is not secure itself. Even though it is a bit more complicated, we recommend making the changes manually as described here.
Attention: Make a backup of your website before performing the following steps or get the help of an expert.
- think about a new address (e.g. “mynewloginURL”), which you want to use for logging in later.
- go via (S)FTP access to your WordPress root directory. There you will find the file “wp-login.php”. Copy it to your computer and open it with a text editor.
- search for “wp-login” and replace all hits (13) with the made up “mynewloginURL”.
- save the file as a new file with the filename “mynewloginURL.php” and upload it via (S)FTP to the same directory where “wp-login.php” is located.
- exit the (S)FTP session and go to the WordPress dashboard.
- navigate to “Appearance” and click on “Theme File Editor”. Open the “functions.php” file.
- copy the content to a text file & save a backup copy.
- Scroll to the end of the file and paste the following code.
- Replace “myCustomLoginURL” with the name you gave earlier.
- Click on “Update file” to save the changes.
Congratulations! Your new login page is now available at https://www.yourdomain.com/myCustomLoginURL.php.
Pro Tip! If possible, use a so-called child theme to make the changes to the “functions.php”. A child theme has its own isolated “functions.php” for the simple reason that you can make changes there and the main theme remains unaffected. This means that theme updates can be done without any problems and your changes will not be lost. Premium themes usually come with a child theme that you can install and activate after installing the main theme.
Your new login page is now good to go and will drastically reduce the number of unauthorized access attempts. However, a user will still be redirected to the new login page by default when entering the default WordPress login link. To prevent this, we recommend 2 options.
1. delete the old “wp-login.php” from your server
The disadvantage of this method is that a 404 message (file not found) will be generated every time a request is made to the web server, as the file no longer exists. Each 404 message can have a negative impact on search engines. So try to avoid them.
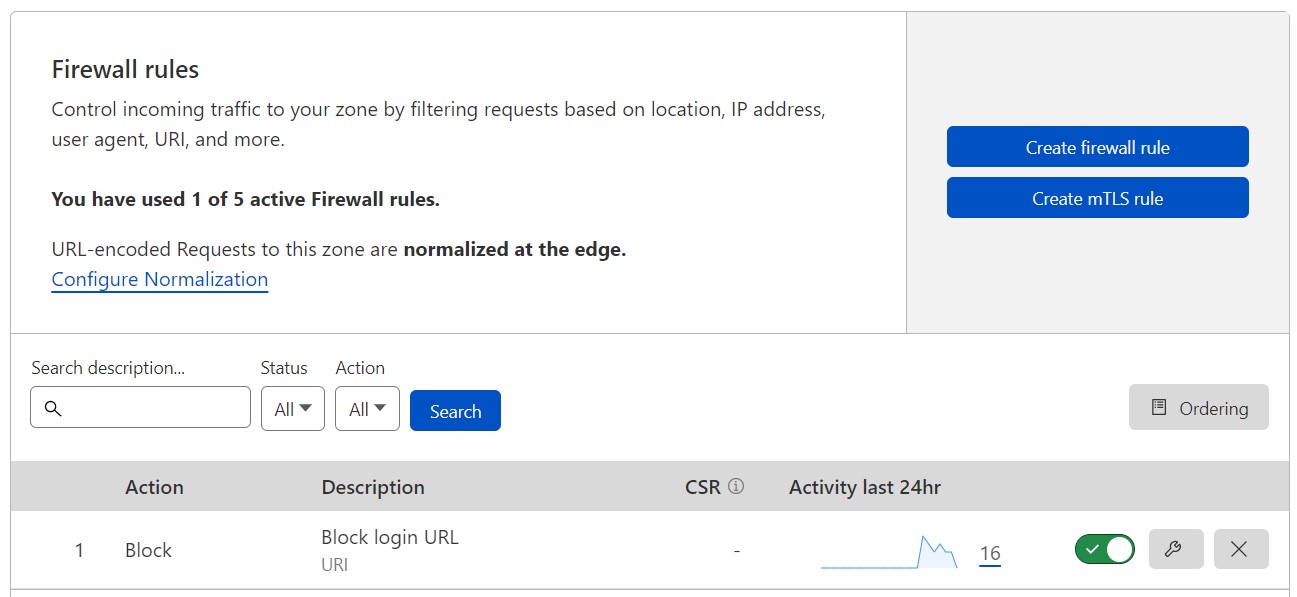
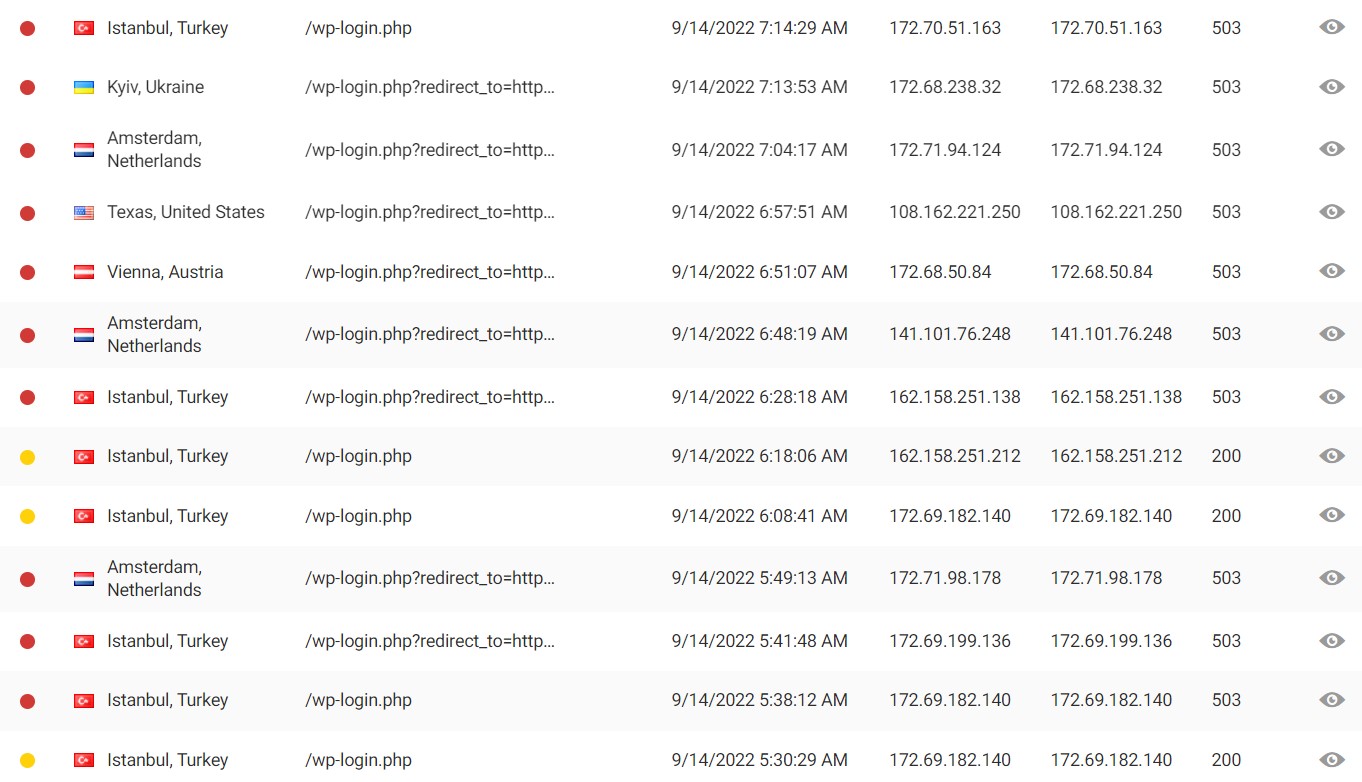
2. better: use a firewall (WAF) and create a rule that denies all requests for the default login.
Consider using a service like Cloudflare or Sucuri. Besides significant performance improvements for your own website, both providers offer a great protection against all common attacks. There you can easily create an additional rule that completely prevents access to the old “wp-login.php”. Your first line of defense.
In this example you can see that shortly after the activation of the new firewall rule many attempts were made to unsuccessfully access the old login link “/wp-login.php”. The HTTP status message returned to the caller changes from 404 (not found) to 503 (unavailable) due to the firewall rule. In addition, a user will be automatically blocked if he continues to try to access this URL. This is signaled by the red dot. Well dear brute force hackers. Nice try, but bad luck guys 🙂
Limit the amount of login attempts
As a final security barrier for the login area, we recommend limiting the number of attempted accesses to your WordPress login. Again, this can be easily done using a security plugin like Wordfence even in the free version. For example, you can set a user to be blocked for a certain amount of time or even permanently after 5 failed login attempts. Wordfence even allows you to track all traffic live and have email notifications sent to you about unauthorized attempts.
9. Encrypted Connections (SSL)
Please do not run a website without installing an SSL certificate. These are already available for free (Let’s Encrypt) and are perfectly sufficient for many.
Pro Tip: We recommend making sure that these free SSL certificates are supported when choosing your hosting provider!
Communication (data exchange) between web-based applications such as your website and a user’s browser takes place via the unencrypted (H)yper (T)ext (T)ransfer (P)rotocol “http://”. Installing an SSL certificate enables the SSL (Secure Socket Layer) indicated by an “s” (“https://”) and a closed padlock on your browser. The data is now transmitted in encrypted form.
Advantages of SSL certificates
1. Security
The most important reason for an encrypted data transfer is of course, as already mentioned, the additional security.
What can happen when online banking data is sent unencrypted? Hackers can intercept this communication and read out sensitive data, since it is transmitted in plain text. This particular hacking technique is also known as MitM (man in the middle attack) mentioned above. We want to avoid this at all costs!
2. SEO
For search engines like Google, “https://” is an official ranking factor. Google penalizes unencrypted pages with a worse position in the search results. Read more about SEO
3. Trust and credibility
When you come across an unencrypted page, browsers warn you unequivocally about the potential security risk you are taking when you open that page. With the padlock closed on the browser, users immediately have more confidence knowing that their data is being transmitted in an encrypted manner.
4. Performance
Many hosters reward hosted sites that are encrypted with better performance than those without encryption at identical rates.
10. Disable XML-RPC
XML-RPC stands for Extensible Markup Language – Remote Procedure Call and is an interface with which website content can be exchanged with other systems in a structured way.
An example: creating a blog post in WordPress and then transferring it to other platforms that can display the same blog post there.
Because it is outdated, XML-RPC has since been replaced by the much more modern and powerful REST API and can therefore be disabled in most cases. WordPress enables the XML-RPC interface by default for backward compatibility with older applications.
The old XML-RPC interface is a popular target for brute force attacks, as multiple commands can be submitted within one HTTP request.
Therefore, disable XML-RPC. You can easily do this with the help of the free Disable XML-RPC plugin. But it is also possible without a plugin by simply editing the “.htaccess” file in your WordPress installation directory via (S)FTP.
Make a backup of the file first!
Then copy the following text to the end of the file:
Finally, save the file. Done.
11. The File “wp-config.php”
This file is by far the most important file on your site when it comes to WordPress security. It contains your database credentials (in plain text!) and security keys that govern the encryption of information in session-sensitive text files called cookies. Below are some suggestions to better protect this important file.
Important. Make a backup of your website beforehand.
1. Move the “wp-config.php” file
By default, “wp-config.php” is located in the root directory of your WordPress installation. However, you can also swap it out to a directory that is not accessible via the Internet.
- Create via (S)FTP a new directory (e.g. “wp-config”) outside the directory where the WordPress installation is located.
- Create a new text file “wp-config.php” there, into which you copy the contents of your original “wp-config.php”. Save the new file.
- Then replace the content of the original “wp-config.php” with the following code snippet:
<?php include('/home/wp-config/wp-config.php'); ?>where “/wp-config/” corresponds to the previously created folder.
- Save the original file, which now only contains the code snippet reference to the swapped out, new file.
2. update WordPress security key
When WordPress is installed, 4 different keys are randomly generated to improve the encryption of the information stored in the user’s cookies. These are: AUTH_KEY, SECURE_AUTH_KEY, LOGGED_IN_KEY and NONCE_KEY.
Sometimes it is useful to renew them. Especially if you are using an installation as a template or have purchased an application from someone.
WordPress provides a free tool that you can use to generate these keys. You then replace them with the previous keys in your “wp-config.php” file.
3. reduce the access rights
WordPress advises to change the permissions for the file “wp-config.php” to chmod 440 or 400 to prevent unauthorized reading.
However, with some hosters your website will stop working. In this case, simply change the permission back to the original value.
Tip: You can change the file and folder permissions with a (S)FTP program.
12. Hide Your WordPress Version
The less technical details you reveal, the harder you make it for an attacker. By default, the WordPress version is displayed in the header of the generated HTML code of your website.
You can easily turn off the version display with a security plugin like Wordfence or by adding the following code snippet to your theme’s functions.php file.
See point 8. for where to find and edit the file.
13. WordPress Security Plugins
To increase the security of your website, there are great solutions like WordFence that offer a lot of protection and other useful features even in the free version.
Here are some features:
- Force the use of strong passwords.
- Force passwords to be changed on a regular basis.
- Logging of user activities
- Update WordPress security keys
- Malware protection and detection
- Two-factor authentication
- reCAPTCHAs (protection against spam and login forms)
- Web application firewall (WAF)
- Live traffic viewing and monitoring
- Automatic threat blocking
- Instant logout and blocking of suspicious users
- IP whitelisting and IP blacklisting
- File change detection
- DNS change monitoring
- Malicious network blocking
- WHOIS information about visitors
- Automatic e-mail notifications
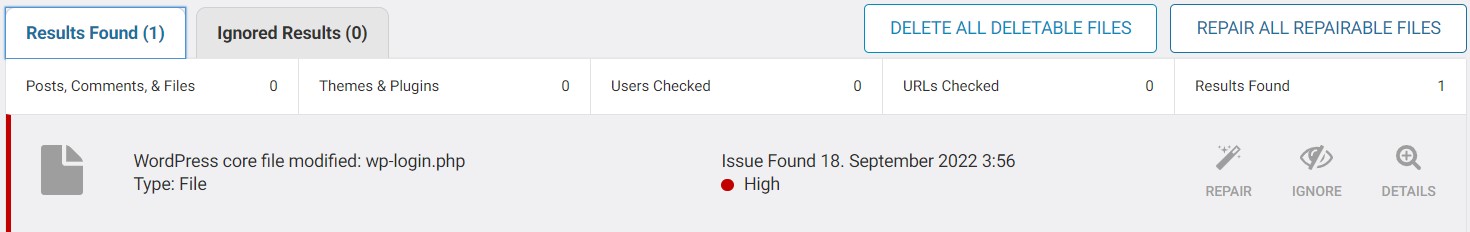
Detecting changes to important files and identifying malicious files are great features, as any change or modification to files can indicate a hack.
Since we have previously changed the content of the file “wp-login.php”, our Wordfence monitoring software has automatically detected this change. If we want to keep the changes we made, we can tell Wordfence to ignore this file. Alternatively, there is a possibility to restore the original file. Very useful!
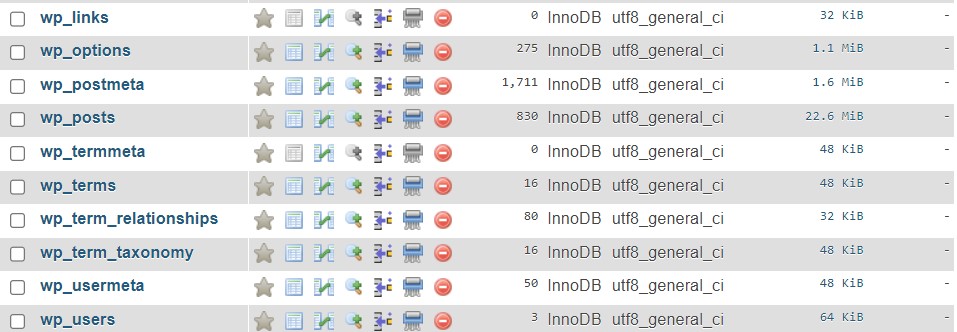
14. Database Security
When installing WordPress, the installer asks for information about the database you want to use WordPress with. Usually, you have already created it in your hoster’s backend or they have done it for you.
Pro Tip: The login information for the database should always be different from the WordPress login information!
If you create databases manually, we recommend that you assign a database name that is not easy to guess. The same goes for the username and password. Do not use the WordPress login data!
When creating the database, you can also change the so-called table prefix. By default, this is always “wp_” and indicates that it is WordPress database tables and data. And of course the bad guys know this.
15. FTP Connections
FTP means File Transfer Protocol and gives you the ability to directly manage the folder structure and files on your site as you would in Windows Explorer or MAC Finder.
As always, use secure usernames and passwords that are used exclusively for this FTP access.
Use the encrypted Secure FTP Protocol (SFTP) if your hoster supports it.
As a rule of thumb, unencrypted connections will transfer data in clear text. Even login data! An easy target for the attacker. Therefore, if possible, always use secure connections.
16. Check WordPress file and folder permissions
When installing WordPress, general permissions are assigned to files and folders. These usually provide sufficient security.
How you can further increase file/folder security as described in this great article.
But beware. Assigning permissions that are too restrictive can affect the operation of your website.
Basic file and folder permissions
- Read only, to give users the right to read a file.
- Write to give users the right to write or modify the file.
- Execute to give users the rights to execute a file (script).
The same concept applies to folders. However, assigned folder rights apply to all files in that folder (rights inheritance).
Tip: You can change the file and folder permissions with a (S)FTP program
17. Use a Content Delivery Network (CDN)
CDN stands for Content Delivery Network and provides excellent Internet security services, fast distributed DNS services and sophisticated caching mechanisms that provide an enormous performance boost. The CDN is located between the visitor and the hosting provider or your website and acts as a so-called reverse proxy.
A CDN like Cloudflare or Sucuri is one of the best solutions to protect yourself against DDoS (Denial of Service) attacks. A DDoS attack aims to cripple your web server for a certain period, so that it cannot process any more requests because it is busy with the attack.
To use a CDN, you need to register your own website and make the appropriate DNS settings for your domain there. From now on, the CDN will take over the DNS resolution and process requests to your website. For this to work, you just need to create an A record for the top-level domain (e.g. yourdomain.com) and CNAME records for the subdomains (e.g. www.yourdomain.com) in the DNS settings.
During the configuration, the CDN assigns 2 new DNS servers, responsible for the fast name resultion of your website. Log in to your domain registration provider (where you purchased the domain) and replace the existing DNS servers with the new DNS servers of the CDN.
Once properly configured, the CDN receives, analyses, evaluates and processes all requests.
We are happy to assist you with the setup of CDN and DNS.
Explanation of DNS (Domain Name Service)
Communication between devices on a network is done using the Internet Protocol (IP).
Devices such as web servers, laptops or cell phones that are on this network are assigned so-called IP addresses either manually (static) or automatically (dhcp). This IP address consists of a series of numbers that identifies each device.
But now imagine that instead of the name www.google.com, you had to remember the IP address of Google and type it into your browser. Unthinkable!
In this context, the DNS works much like a large directory assistance system. You know the domain (the name of a computer on the Internet that you can remember) – so for example www.google.com. You send this as a request via your browser to the Internet. The domain is then translated by the DNS into the corresponding IP address (the “connection number” on the Internet) and sent to the correct computer, which answers your request.
The faster this service can perform the name resolution, the more positive effect it will have on the performance of your website. The servers of CDN providers are among the fastest in the world.
Summary
We have shown you many ways to improve your WordPress security. Strong passwords, regular maintenance and choosing a securely managed hosting provider are just some of them.
So, take the time and implement some of the above security tips before the worst happens and you might lose important data.
Do you have any questions, suggestions or comments? Please get in touch!